In addition to security problems that are already inherent in the design of a system, there are also many ways to attack a system concretely in its deployment in practice. These attacks range from exploiting implementation errors to unexpected side effects of the system in its context of use to unjustified security assumptions on subcomponents.
Furthermore, hardware solutions can efficiently handle security-related problems: for example, a secure hardware enclave ensures that the computation has 'not been tampered with'.
Part of practical security is so-called 'side-channel attacks'. Here, for example, the power consumption of the processor is used to read the cryptographic key, as the encryption performs different computations depending on key bits 0 or 1.
In the VE-ASCOT project, we are doing research with industry and research partners how a system can check its integrity and uniquely identify components.
In the KASTEL Energy Security Lab, we are working on practical solutions for the secure operation of the power infrastructure. This includes, for example, cryptographic (tamper-resistant) communication of measuring devices in substations.
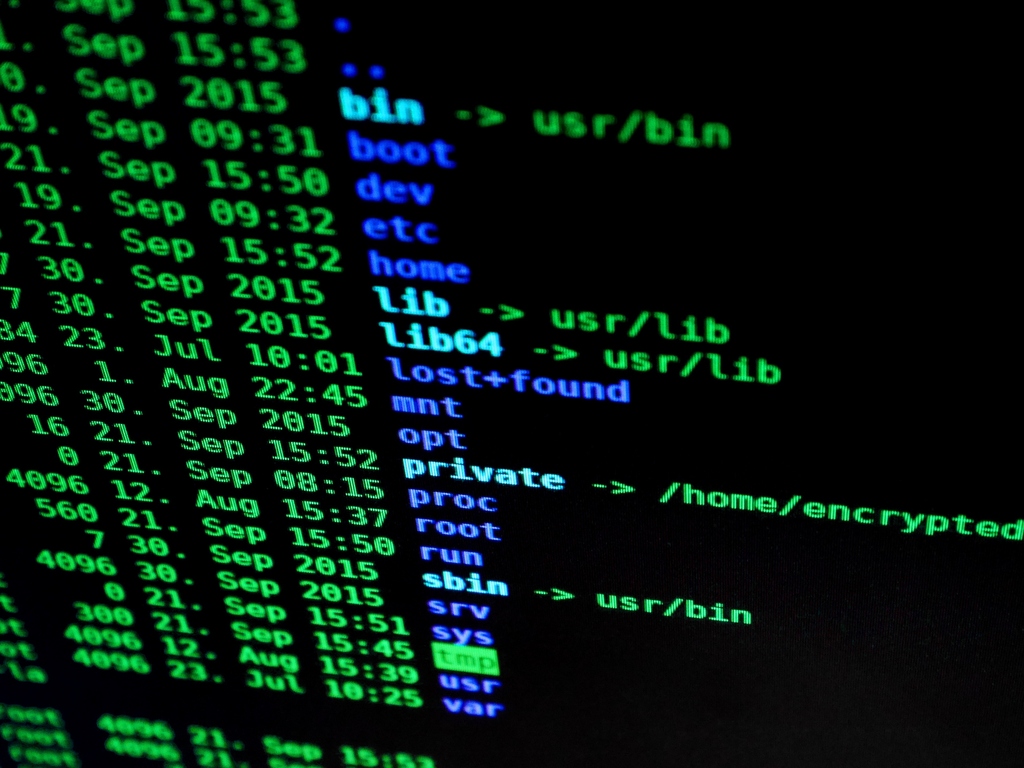
In the application security lab, students can attack a number of vulnerable applications to get a password from them (capture-the-flag tasks). In this way, students learn the consequences of simple programming errors such as buffer overflow, use-after-free, race conditions, or integer comparison bugs, which in the worst case can allow an attacker to execute arbitrary code.
